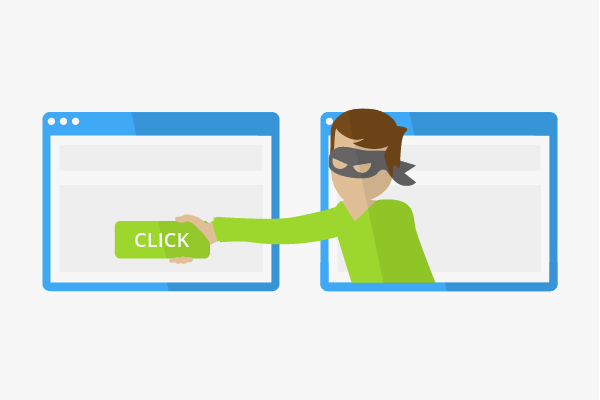
Clickjacking
Clickjacking, also known as UI redressing, is in the click fraud category and is a method used by criminal hackers to make users unknowingly perform certain actions by clicking on buttons or links. The objectives of clickjacking include the control of other people’s PCs as well as the redirection of users to paid content or fraudulent websites. Today, many large portals, such as Facebook, have to come up with measures against clickjacking.
Background
The display of a web page in the browser is as a result of the retrieval of a file from the server. Other scripts, such as JavaScript applications or even frames, are also loaded depending on the scope of the web offer. On the one hand, this enables an improved functionality of the website. On the other hand, these applications provide ideal gateways for click fraud. With clickjacking, the user is shown content that he/she can click on. However, upon clicking on the displayed link, the hacker’s activities are initiated in the background instead of loading the actions shown in the foreground.
Possible forms of attack
Clickjacking can be implemented by hackers in various ways. In most cases, this is done through the misuse of JavaScript applications:
Browser games
Here, the users in the foreground click on game elements that change the configurations of their computers or browsers, which in the process makes them more vulnerable to hackers.
Download buttons
These are used by Internet fraudsters to lure the user to click on a download link. The link then loads malicious programs in the background.
All activatable buttons
With frames, every button on a website can basically be manipulated to make the user unknowingly trigger the actions desired by the hacker.
Objectives of clickjacking attacks
- Spying on users
- Stealing sensitive data such as passwords and account information
- Redirecting users to websites with harmful content
- Enforcing payment subscriptions
Possible defense
The commonly used browsers have numerous opportunities of unmasking clickjacking. Similarly, anti-virus software with integrated browser protection can also be used to prevent possible attacks. The WordPress CMS blog has also offered protection against UI redressing since 2011.[1] Here, it is often checked whether the pages are allowed to use frames or not before loading them. Likewise, it may be advisable not to automatically allow JavaScript for all sites.
Facebook and clickjacking
Social networks are also affected by the clickjacking problem. In this case, the clickjacking technique is used to make users who click on a link automatically become Facebook fans of a Facebook page. However, the network reacted very fast to this trend and has taken up legal measures against clickjacking methods that fraudulently collect Facebook fans since 2012.
References
- ↑ WordPress 3.1.4 gets Clickjacking Protection internetnews.com Accessed on 03/02/2014