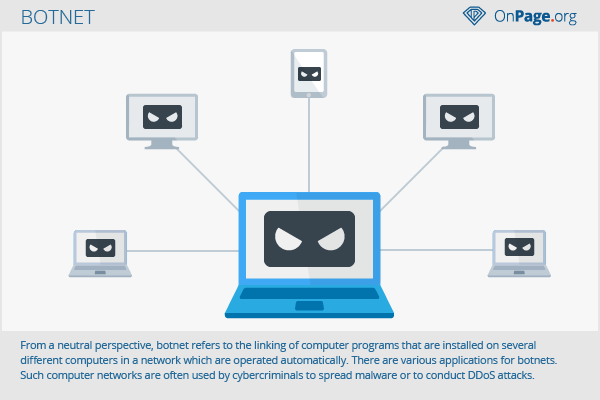
Botnet
From a neutral perspective, botnet refers to the linking of computer programs that are installed on several different computers in a network which are operated automatically. There are various applications for botnets. Such computer networks are, however, often used by cybercriminals to spread malware or to conduct DDoS attacks.
Background and dissemination
Large computing operations such as data mining for creating Bitcoins require large computing power. Just one computer or server network is often not sufficient. In such a case, a botnet is a solution because the computing tasks can be distributed to many individual computers.
On the negative side, this bundled computing power has been used to launch attacks against websites or to distribute massive amounts of webspam or email spam.
Spreading
The establishment of a botnet is called spreading. If the individual users in a large computer network have not installed the bot on their own accord on their computers, then criminal activities have used other techniques to install bots. The infected computers are also called “zombies.”
One technique for installing a bot is malware. It is sent via spam email to as many mail addresses as possible. If you open the link contained in the email or the attached file, a program gets installed, with which several functions of the computer can be controlled remotely.
Infected sites with download offers are another method of how botnets get established. A Trojan will be installed on the computer as part of a download.
But even without direct intervention by a user, a bot may be introduced on another computer by exploits. Software or browser vulnerabilities are exploited. An exploit can also occur by accessing an infected website.
Usage
Different services are available through a botnet. Each established network can also perform various functions in sequence. The following actions are possible, for example:
- Bulk sending of spam or phishing emails
- Attacks through a proxy server
- Downloading and running programs on the infected computer to perform additional operations or to optimize the botnet
- Executing DDoS attacks: A large network of zombie computers will execute millions of requests to a server and thus crash it.
- Click fraud: In this case, other computers are used to click on ads or banners, for which the publisher will then be paid. Because of the different IP addresses and computer types, this form of click fraud is very difficult to prove.
- Attacks within the botnet: The infected computers will be scanned for important passwords or other sensitive data, which are then sold by criminals.
- File sharing: A botnet provides enough space for illegal data material such as pirated movies or pornographic material.
Legal application:
- Mining of Bitcoins
- Calculating of scientific data
- Rendering of films
Types
There are various types of botnets. But they all contain command-and-control servers which are controlled from a central computer (operator). There are several channel options to control the bots:
- IRC
- Web-based tools
- FTP
- P2P
Some of these channels can also be combined with one another, making it difficult for investigators to identify the author of the established network. In some cases, law enforcement agencies have nevertheless gotten lucky, such as in 2010, when the notorious botnet “Mariposa” was uncovered.
Hazards
Because of their high computing power and sheer mass, botnets can bring even large websites to their knees using DDoS attacks.[1]Therefore, it is important that every user works to protect their PC against attacks through malware or exploits. Thus, the Federal Office for Information Security repeatedly warns against infection and the associated data theft.
References
- ↑ Group used 30,000 node botnet for MasterCard and PayPal attacks pcworld.idg.com. Accessed on 05/07/2014