Spam
Spam can be defined as unwanted messages that are mainly sent electronically. They are delivered without having been requested by the recipient. It is usually advertising. There are various types of spam, such as email spam or spam on social networks. Those affected can turn to the designated points of contact and seek help.
Detection of spam
Spam has many characteristics by which it can be recognized. Such indicators in an email should caution you. In order to protect against spam damage, conspicuous features in emails should be cause not to open any attachments, etc.
Salutation
Most spam emails don’t contain a salutation. Phrases such as “Dear Customer” or “Dear Sir” are used because the sender does not have the full names of the recipients. Professional companies, on the other hand, have the full names of customers and also address them with it. Therefore, lack of a salutation is often sufficient as an indication of a spam mail.
Content
The content of spam messages is often written in bad English or they are grammatically incorrect translations generated with an online tool. They differ very much from real company communication. Respectable companies whose first language is not English write their messages to English-speaking customers in good English.
Key terms
Particularly during the beginning periods of spam, terms of a vulgar nature were often used or terms from the medical field. The most notorious spam advertising comes from Viagra. In order to avoid spam filters, applicable words may get modified. Alternative spellings would include. VIAGRA, V! Agra, Vi @ gr @ or V-I-A-G-R-A.
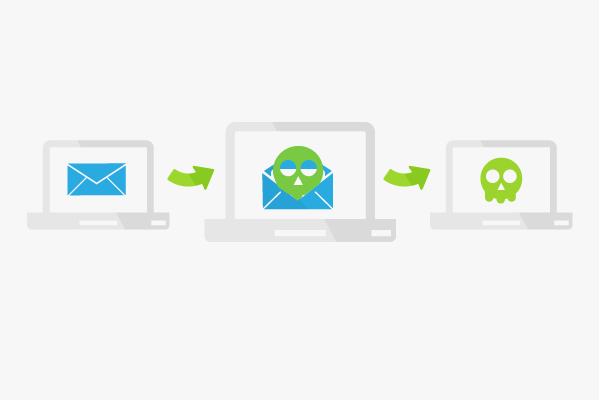
Attachments
Spam email attachments are dangerous. Nowadays, such emails are intended to cause damage to the recipient. An attachment opened by the recipient can contain malicious programs.
Files such as .pif, .exe, .xls, .ppt, and .docs are started with a single click. If an attachment is opened, the malicious program is immediately executed. The purpose of some malware is to spy on users and get their passwords. Phishing can also be initiated via attachments.
Email body
One feature of spam is that they have a whole HTML body. This means that extremely large font or font color can be used. The layout of the email is much more colorful and more eye-catching than “regular” email.
Sender and reply address
If the sender is a company employee, the sender’s mail address should be checked. There are often cryptic sections with endings such as @aol.com, @hotmail.com. It can also happen that friends have been victims of attacks and their email addresses are used as senders. Attachments or links from known senders should therefore not be opened, if there is even a fraction of doubt concerning the authenticity of the content. It should be questioned whether a friend would actually send an email of this kind, with this language style and this address, etc.
Links
Spam messages usually contain at least one link. If this is clicked on, it shows the sender that the recipient address is still active. This can result in increased spam messages. Other links may direct the recipient to a customer website. The unsolicited sending of such commercial emails is, however, forbidden and punishable. The links may also direct to sites that are a high risk of coming into contact with malicious software.
Ideally, links should not be clicked. However, spammers trick you with link texts as well. There may be a difference between the link text and the actual URL. Before a link is clicked, you should hover your mouse over it. Depending on the browser setting, the actual URL will be displayed at the bottom. This address is easily recognizable as spurious in the case of spam messages. It makes no sense and does not allow conclusions to be drawn about the actual company.
The ending can also be revealing, because many of these addresses are registered abroad and their address ends with .ru for Russia for example. Images can be embedded as a link as well. The same applies here, check the destination URL before clicking.
Types of spam
Spam messages are sent not only by email, but can also be sent as a personal message via social networks or Skype. It can even be in the form of verbal communication on the telephone.
Email spam
- Unsolicited bulk email
This is the most popular type of email spam. These are emails which are sent to as many recipients as possible. Such messages usually contain advertising, but can also consist of hate-inciting or missionizing content.
- Unsolicited commercial email
These emails consist of commercial content, which is sometimes sent to individual recipients. Dubious, cheap deals on sex, potency or illegal online gambling casinos are typical examples.
- Collateral spam, backscatter
In this case, non-delivery messages are generated and assigned to a third, completely uninvolved email address. This is specified as the sender address by the sender in advance.
Search engine spamming
In this case it is attempted to positively manipulate the evaluation algorithm of a search engine by means of targeted entries on foreign or one’s own websites in order to achieve the best possible ranking in the search results.
Phone spam
Communication via the Internet telephones and mobile phones can be disturbed by spam. If an affected person picks up on an Internet telephone call, audio data are automatically played back. In mobile phone spam, usually unwanted short messages are sent or calls get made. Another version are ping calls. These usually last only a few seconds and urge a call back, which is then very expensive for the caller.
Social networks
In spam on social networks, the search options of the networks are used mainly to target specific target groups or individuals. There are also programs that search for public profiles in social networks. These are sent contact requests in order to send messages. Fan pages or fan groups are another easy way to send spam messages.
Such messages then usually contain a link to a pornographic website, advertises for products or infect the computer of the person concerned. One trick is sending out messages on behalf of Facebook Security. The accusation is that the recipient has violated the guidelines and he now has to confirm his profile with a link. The link directs to a phishing page. The queried data does not go to Facebook, but to fraudsters. In addition to name, email address and password, credit card numbers are also asked for.
Spam via instant messaging
Spam occurs with instant messaging services like msn and icq as well. Account names are often written on the Internet to allow others to connect. This means that fraudsters are also able to get the name and contact the person. An example is the message “are you sure you did not upload these photos?” followed by a link. The receiver will arrive on a phishing page, on which he is supposed to enter data.
How spam gets distributed
Spam messages are usually not sent by the spammers’ servers. Infected or remote-controlled servers are used for this purpose. This affects poorly administered workstations and privately owned computers. Another option that the spammers utilize, is distribution by providers from abroad. These are countries in particular with a very low risk of legal prosecution or where complaints are ignored by the authorities that are getting paid off for it by the respective spammer.
Origin of the data
App Store for Android
Spammers can build apps that are fast to program and make sure they’re bought. Since you have to specify the correct name and email address when you buy an app on Google Play, the spammers will get a large amount of data.
Trojan apps on smartphones
Trojan apps, which are generally rated well, access the entire mobile phone’s address book and forward the data over the Internet. If the telephone is synchronized with a computer, the data of the PC is also forwarded.
Social networks
On social networks like Facebook, it is possible to offer third party apps. Registered app developers can access the data from Facebook users, even if they have not installed the app. Since it is possible to pass yourself off as a developer, the spammers have yet another way to obtain a huge database with names and email addresses. If an app is actually installed, the user must agree to the data transfer.
Data leaks
Again, and again, data leaks occur at renowned companies as well as in cloud services. In these cases, spammers have access to a large part of the data. On top of that, internal employees also have access to the data and sell it to spammers if the price is right.
How to avoid spam and get help
Spam filters are a very popular and efficient measure against spam. Another possibility is to create a temporary email address, which is always used when a service requests an email when you log on. In order to protect your contacts from spam, it is usually useful not to send emails to a large number of contacts and to enter the contacts only in the BCC field. This prevents that all recipients can see all addresses. It is important not to reply to suspicious emails. This confirms the existence and regular use of this email address, which could result in increased spam. Since January 2007, complaints have been accepted by the Internet complaint office of the eco Association of the Internet Industry. Complaints about telephone spam can be filed in Germany with the German Federal Network Agency, which then carries out a traceability and accurate review.
Impact of spam
Spam is causing serious damage in the global communications system. The additional data result in considerably more processing effort. Furthermore, reading and sorting spam is costly, spam filters have to be purchased and maintained, and costs are generated for every transferred byte of spam, since Internet service providers usually charge for their services based on the transferred data volume.
According to a study from 2009, 100 billion hours of work time and 33 billion kilowatt hours of energy are spent on viewing and deleting 62 million spam emails.
Web Links